You can also watch this video on lbry
- Security researcher discovers 44% of people in Tel Aviv, Israel use their phone number as their WiFi password
- This makes cracking a network's password quick and easy
- He collected 5000 WiFi password hashes via wardriving
- Of these, 2200 were crackable within just 10 minutes
Lightbulb Moment
In a new blog post, Ido at cyberark explains how after having asking neighbours if he could use their WiFi on a few occasions he realised people often use their phone number as their WiFi password.
This led to his hypothesis that if he hadn't got lucky and a good chunk of people really did use their phone number as their WiFi password, it should be quite easy to crack a large percentage of his hometown's (Tel Aviv) WiFi access points. An Israeli phone number consists of 05 followed by 8 random numbers, as such there are 108 or 100 million possible combinations - a tiny number in the world of password cracking.
Wardriving
Ido set out on a wardriving mission to collect a few thousand PMKID hashes. Many routers come misconfigured by default, emitting PMKIDs which are typically used in mesh networks to facilitate a device hopping between access points.
A vulnerability discovered in 2018 made it possible to crack PMKIDs to find the original WiFi password.
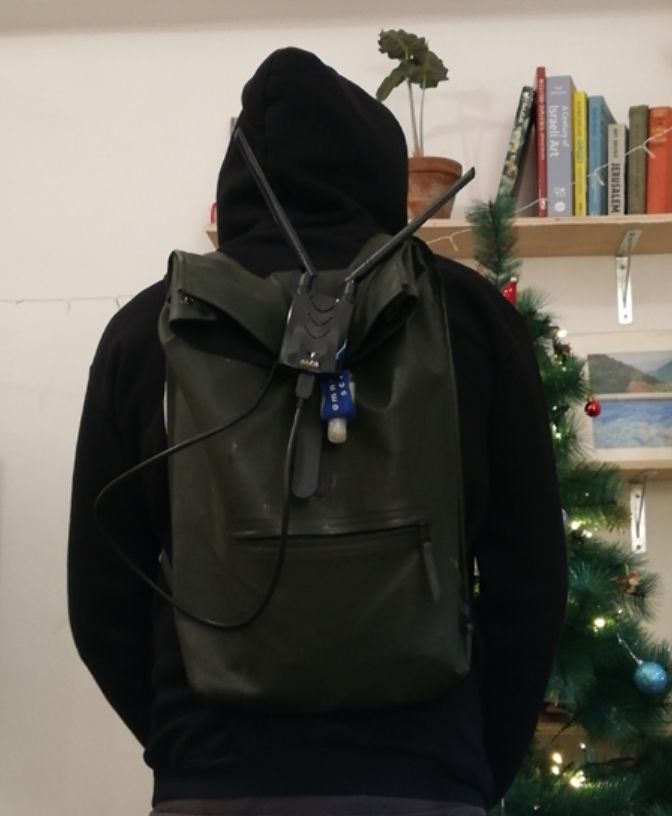
Ido's wardriving rig consisted of an Ubuntu machine hidden in a backpack, along with a an AWUS036ACH ALFA Network card. Not looking completely suspect, Ido roamed his neighbourhood picking up 5000 PMKID hashes in total
Cracking
Using the GPU cracking tool hashcat, Ido discovered that 44% of the networks had used a phone number as the password. A laptop was able to crack these in 9 minutes.
By putting the remaining hashes through a dictionary attack using the infamous rockyou.txt password list he was able to crack a further 900 hashes. After putting the rest through some more incredibly basic cracking techniques he was able to crack in total, 70% of his original hash list, an impressive result.