You can also watch this video on LBRY
- New book alleges booking.com was hacked by a US intelligence agency
- The website apparently opted to keep the breach a secret
What We Know
Booking.com - a website for booking hotels and flights - discovered a breach in 2016, “The breach involved names of Booking customers and their travel plans.”. After months of analysis it was determined that an individual named "Andrew" was behind the intrusion, he works for a company known to carry out operations on behalf of US intelligence.
In the wake of the hack, the website took legal advice which resulted in them not disclosing the hack to their customers or authorities. As the breach took place before GDPR was a thing, laws surrounding disclosure were murky and open to interpretation..
We don't know much more than this, the vague accusations and lack of specificity or evidence have led some to suggest that this story is being inflated as a publicity stunt for the Authors' new book.
Why Hack a Travel Company?
At first hacking a travel company sounds a little odd and pointless. However travel companies are privy to information of who will be where and when. If their databases can be successfully hacked an intelligence agency potentially catch targets outside of their natural habitat, bug their rooms, follow them around, etcetera. Targets could include those on terrorist watch lists, foreign officials, diplomats or even influential businesspeople.
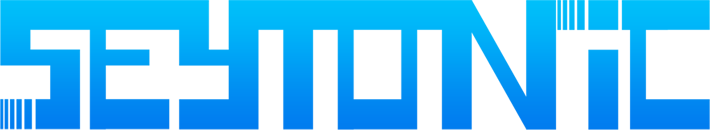
A prime example of this in action are the documents leaked by Edward Snowden in 2013 which revealed a top secret operation helmed by UK spy agency GCHQ - "Royal Concierge". The operation focused on monitoring the hotel bookings of foreign officials all over the world.
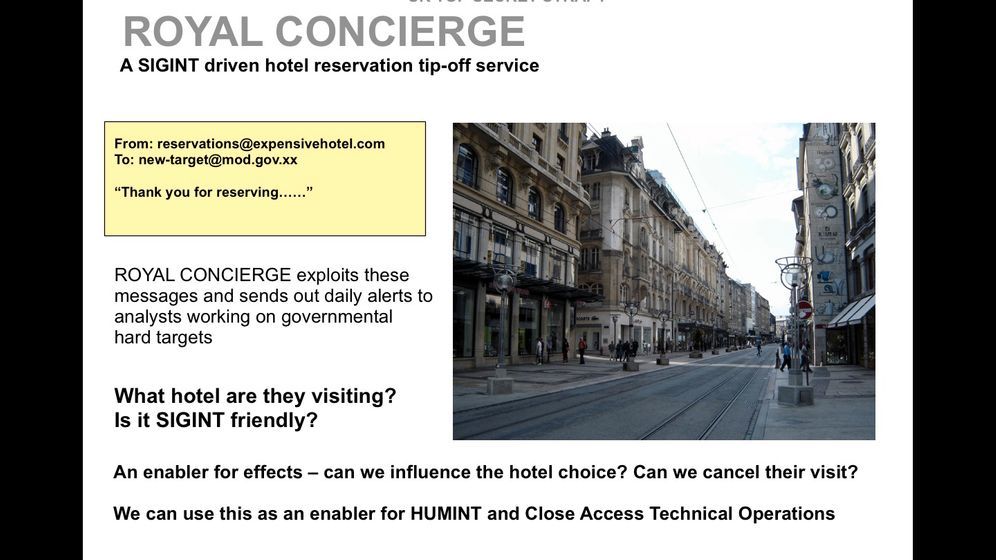
Leaked powerpoint slides marked "top secret" show that the agency had some kind of a system in place to monitor booking made by those with email addresses ending in '.gov' - an extension typically used by diplomats.
From partially redacted logs you can see hotels in Zurich, Singapore, Hong Kong and even the UAE were targeted. logs you can see hotels in Zurich, Singapore, Hong Kong and even the UAE were targeted. The aim here, to gather information for what’s described in the document as “human intelligence and close access technical operations”, in other words, operatives on the ground could bug and surveil targets. In response to the leaks, GCHQ said that it "neither confirms nor denies the allegation."